Polymorphic attacks: the shape-shifting threat

Cofense
- Published
- Cybersecurity, Technology

Malicious email threats were once a numbers game, reliant on repetition and scale. AI-powered polymorphic phishing has rewritten that model, replacing volume with relentless variation as every message, link and attachment is uniquely generated in near real time. Here, Cofense examines how this machine-speed evolution is outpacing traditional email defences and sets out five practical measures organisations can take to strengthen detection, accelerate response and reduce exposure
For years, security teams relied on spotting repetition: identical subject lines, reused domains, recognisable patterns. Polymorphic phishing shatters that model. Instead of sending the same lure at scale, attackers continuously alter emails, tweaking sender names, wording and links so no two messages look alike.
Cofense’s latest report shows these changes can occur every 15–20 seconds, enabling attackers to test defences in real time and adapt faster than traditional controls can respond.
Artificial intelligence now sits at the core of the attacker workflow. Generative models allow threat actors to instantly produce thousands of unique yet convincing variations of a campaign, refine language, personalise content using public data, and test what bypasses security controls, all at machine speed.
Cofense research shows that in 2025, 76 per cent of initial infection URLs were unique and 82 per cent of malicious files had unique hashes, even when delivering the same payload or sharing IP addresses. This level of variance reflects AI-driven automation.
The speed of evolution makes polymorphic phishing especially dangerous. Attackers iterate in minutes, not days. By the time security teams update rules or blocklists, campaigns have morphed. Many attacks also specifically evade analysis by displaying different content depending on device, browser, or perceived security tooling. Traditional perimeter defences may block known threats, but polymorphic campaigns are built to slip through, leaving a narrow response window.
To counter this reality, organisations must rethink defence strategies. Five tactics stand out:
The first is to prioritise post-delivery detection and response. Polymorphic attacks are designed to bypass static, rule-based controls by constantly changing. Relying solely on these perimeters creates blind spots once messages reach the inbox, making it vital to have the visibility and resources to act quickly against evasive threats.
The second is to strengthen employee reporting. Cofense research consistently shows the most dangerous emails are those identified by employees reporting from their inbox. Organisations should make threat reporting fast, simple, and encouraged. Well-trained employees act as distributed sensors, spotting subtle anomalies that machines miss, especially in highly variable, AI-generated attacks.

The third is to ensure training reflects real-world polymorphic threats. Generic or randomised phishing simulations do not prepare users for campaigns that continuously evolve. Training should reflect current and active threats seen within the organisation’s industry, conditioning users to recognise how genuine polymorphic attacks look and behave. When employees understand the tactics, pace and variability of these campaigns, they are far more likely to identify and report suspicious activity quickly.
The fourth is to reduce response time through automation. Users often engage with emails within seconds of delivery, leaving little margin for manual investigation. Organisations should combine user-reported intelligence with automated analysis to identify related variants, search inboxes and quarantine malicious messages at scale before damage spreads.
The fifth and final tactic is to focus on behaviour and infrastructure rather than surface indicators. When every URL and file appears new, detection must centre on how attacks operate. AI-assisted analysis, supported by human validation, will help uncover shared tactics, reused infrastructure, and evolving behaviour beneath polymorphic surface changes.
Polymorphic phishing is not a future risk but the current state of email-born threats. Organisations that fail to evolve beyond perimeter-only defences will remain one step behind.
Further information
Produced with support from Cofense. To find out more about its enterprise-grade threat-intelligence and phishing-response services, visit www.cofense.com
READ MORE: ‘AI-driven phishing surges 204% as firms face a malicious email every 19 seconds‘. Cyber criminals are using artificial intelligence to flood inboxes with near-undetectable phishing emails, recycling the same hidden infrastructure while making every attack look brand new.
Do you have news to share or expertise to contribute? The European welcomes insights from business leaders and sector specialists. Get in touch with our editorial team to find out more.
TOP STORIES
-
 NASA to send rabbit-like drones to scout site for first Moon base
NASA to send rabbit-like drones to scout site for first Moon base -
 Apollo, Artemis, Ali and Live Aid satellite station set for new Moon role in £37m deal
Apollo, Artemis, Ali and Live Aid satellite station set for new Moon role in £37m deal -
 Four forces reshaping cyber risk in 2026
Four forces reshaping cyber risk in 2026 -
 Siemens expands rail technology arm with Italian deal
Siemens expands rail technology arm with Italian deal -
 Italy draws global tech investors as Europe races to build its own champions
Italy draws global tech investors as Europe races to build its own champions -
 Opel turns to Chinese EV technology for new European-built SUV
Opel turns to Chinese EV technology for new European-built SUV -
 Japan and Luxembourg deepen space ties as lunar race gathers pace
Japan and Luxembourg deepen space ties as lunar race gathers pace -
 Polymorphic attacks: the shape-shifting threat
Polymorphic attacks: the shape-shifting threat -
 ‘Lost’ zip design could give space exploration a lift
‘Lost’ zip design could give space exploration a lift -
 Orbitae - AI by SDG Group launches Gena Suite to scale enterprise AI
Orbitae - AI by SDG Group launches Gena Suite to scale enterprise AI -
 Firms ‘wasting AI’ by using it to speed up bad habits
Firms ‘wasting AI’ by using it to speed up bad habits -
 Why leadership matters when implementing AI
Why leadership matters when implementing AI -
 Stratospheric telecoms blimp completes “historic” record 12-day flight over Atlantic
Stratospheric telecoms blimp completes “historic” record 12-day flight over Atlantic -
 Mobile operators warn of higher bills and slower 5G rollout after energy support exclusion
Mobile operators warn of higher bills and slower 5G rollout after energy support exclusion -
 The 2026 European awards cement Steve Durbin and the ISF at the forefront of cybersecurity
The 2026 European awards cement Steve Durbin and the ISF at the forefront of cybersecurity -
 These are the 10 AI trends to watch in 2026 that will drive business forward
These are the 10 AI trends to watch in 2026 that will drive business forward -
 Europe launches ‘anti-kill switch’ cloud shield as Trump fears grip Brussels
Europe launches ‘anti-kill switch’ cloud shield as Trump fears grip Brussels -
 Starmer summons social media chiefs to Downing Street over child safety
Starmer summons social media chiefs to Downing Street over child safety -
 AIMi: bringing intelligence and speed to data migration
AIMi: bringing intelligence and speed to data migration -
 GITEX Africa Morocco to host 1,450 exhibitors and startups as Marrakech event sharpens focus on AI and digital sovereignty
GITEX Africa Morocco to host 1,450 exhibitors and startups as Marrakech event sharpens focus on AI and digital sovereignty -
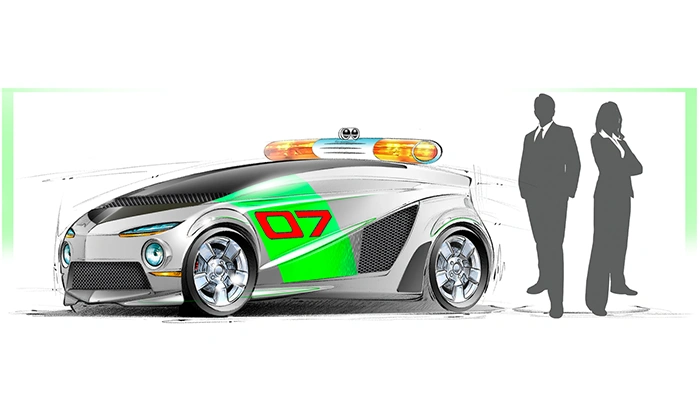
 EXCLUSIVE: LA unveils Ghostbusters-style car to fight post-wildfire ‘toxic soup’
EXCLUSIVE: LA unveils Ghostbusters-style car to fight post-wildfire ‘toxic soup’ -
 Social media giants hit with $6m verdict in landmark youth harm case
Social media giants hit with $6m verdict in landmark youth harm case -
 Former Google executive launches €50m fund targeting Europe’s deep tech scale-up gap
Former Google executive launches €50m fund targeting Europe’s deep tech scale-up gap -
 Airbus to acquire Ultra Cyber in UK defence cyber expansion
Airbus to acquire Ultra Cyber in UK defence cyber expansion -
 UK exposed by cyber omission in Spring Statement as threats intensify, ISF chief warns
UK exposed by cyber omission in Spring Statement as threats intensify, ISF chief warns