Incorporate pen testing-as-a-service (PTaaS) into your tech stack

John E. Kaye
- Published
- Executive Education, Home, Technology

BreachLock has pioneered a bold new cybersecurity innovation that tailors solutions specically to your organisation’s threat landscape
Given the sharp increase in cyber-attacks throughout the COVID-19 pandemic, businesses are starting to rethink their approach to cybersecurity. Most traditional cybersecurity testing methods are cumbersome, limited, and unscalable. Cyber-criminals, by contrast, are using an agile approach to make continuous threats on businesses’ systems and assets. However, a new solution has emerged that will help level the playing eld for businesses: pen testing-as-a-service (penetration testing).
Legacy solutions are either operated manually by cybersecurity professionals or powered by automated so ware. Pen testing-as-a-service (PTaaS) upends this divide. PTaaS automates part of the pen testing process to reduce manual overhead while also leveraging the power of human pen testers. is method combines the intelligence of human experts with the scalability of machines.
PTaaS breaks with the traditional taxonomy of cybersecurity testing solutions. Typically, cybersecurity testing includes three layers of defence: vulnerability scanning, penetration testing (or pen testing), and red teaming. Vulnerability scanning is a passive method for defence that automatically evaluates systems for vulnerabilities at set intervals. Pen testing introduces a human element. Cybersecurity experts seek out weaknesses to exploit. Their findings help DevOps teams find and fix vulnerabilities. Red-teaming is an off defensive exercise in which human experts simulate a cyber-attack. An organisation can then practice responding to the attack. PTaaS consolidates the strengths and addresses the weaknesses of these approaches. e method delivers scalable, continuous, on-demand security.

The pioneer behind PTaaS is a company called BreachLock. Founded by CEO Seemant Sehgal, BreachLock has set out to create a path-breaking alternative to legacy tools and methods.
How does it work?
BreachLock enables clients to request and consume a comprehensive pen test with just a few clicks. By leveraging manual discovery methods and artificial intelligence, BreachLock rejects the “one-size-fits-all” model of traditional cybersecurity. Instead, the platform assigns pen testing programs through its cloud-based so ware that can be tailored to each organisation’s threat landscape.
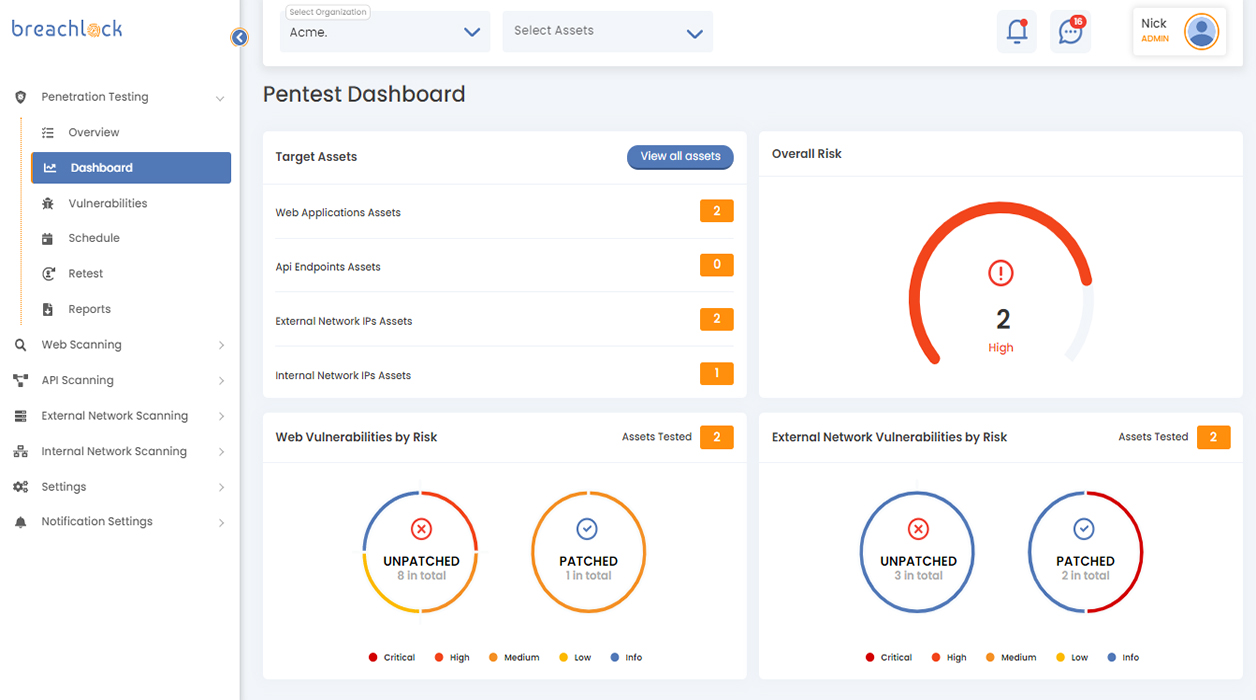
The platform works in four steps. First, when a client is onboarded, BreachLock creates a dedicated workflow for their projects. The workflow contains all the information that the client needs to order and schedule a pen test.
Next, BreachLock conducts human lead pen testing combined with automated techniques. Throughout the pen test, the platform generates offline and online reports so users can view results in real time. These reports facilitate collaboration between a company’s DevOps team and BreachLock security researchers. At any point in the process, if the client has questions about a finding, they can simply reach out to BreachLock’s researchers for support.
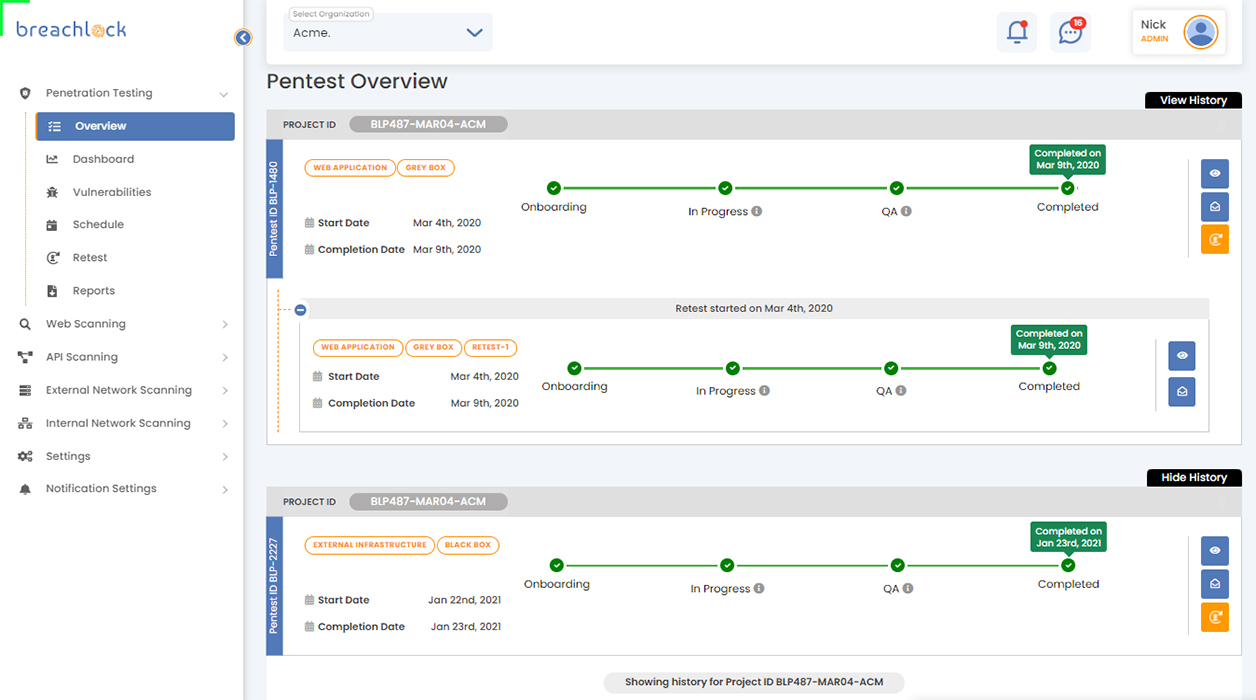
Once the DevOps team has resolved the bugs surfaced by the pen test, BreachLock retests the company’s systems to certify that the vulnerabilities have been xed. In the months following the pen test, BreachLock continuously scans the system for further vulnerabilities. From beginning to end, the client has access to white-glove service from BreachLock’s security experts, who are on hand to provide support.
BreachLock’s reports are structured around recommendations from bodies like OWASP and NIST. As a result, clients can easily leverage BreachLock to stay compliant with SOC 2, PCI DSS, ISO 27001, and HIPAA requirements. Indeed, many of BreachLock’s current customers are enterprise clients who use the platform to satisfy regulatory requirements and avoid costly breaches and fees.
Emerging as a major player
Although the company is still relatively young, BreachLock has already managed to become a major player in the cybersecurity landscape. CIO Review named the company one of their top ten most promising cybersecurity companies, commending BreachLock’s “unique approach that aligns the industry’s best practices that utilise manual as well as automated vulnerability discovery methods.” In 2020, SC Media named BreachLock an “industry innovator for its “mixture of artificial intelligence, the cloud and human hacking.” Enterprise Security named BreachLock one of its top 10 vulnerability management solutions for 2019, and Corporate Vision featured the company as an innovator highlighting the “powerful and easy to use solution.”
Sehgal built BreachLock around a vision of hacking as a philosophy. For Sehgal, hacking is fundamentally about pushing yourself to find new solutions to hard problems, rewarding the worthy, and creating a culture of shared innovation. In keeping with that spirit of innovation, BreachLock is looking to break new ground in the SaaS market and share its technology with organisations worldwide.
PTaaS couldn’t have arrived at a better time. On the one hand, organisations are becoming increasingly aware of the elevated threats they face from sophisticated cyber-criminals, many of whom are employing the same technologies companies use to fight them. On the other hand, federal, state, and local governments are hurrying to pass bills tightening compliance requirements and introducing penalties for organisations that suff er data breaches.
Against this tense backdrop, businesses are searching for security solutions that allow them to achieve continuous testing at scale. It won’t be long before organisations start incorporating pen testing-as-a-service into their tech stack. BreachLock has emerged as a bold new innovator in the space.
For further information:
TOP STORIES
-
 NASA to send rabbit-like drones to scout site for first Moon base
NASA to send rabbit-like drones to scout site for first Moon base -
 Apollo, Artemis, Ali and Live Aid satellite station set for new Moon role in £37m deal
Apollo, Artemis, Ali and Live Aid satellite station set for new Moon role in £37m deal -
 Four forces reshaping cyber risk in 2026
Four forces reshaping cyber risk in 2026 -
 Siemens expands rail technology arm with Italian deal
Siemens expands rail technology arm with Italian deal -
 Italy draws global tech investors as Europe races to build its own champions
Italy draws global tech investors as Europe races to build its own champions -
 Opel turns to Chinese EV technology for new European-built SUV
Opel turns to Chinese EV technology for new European-built SUV -
 Japan and Luxembourg deepen space ties as lunar race gathers pace
Japan and Luxembourg deepen space ties as lunar race gathers pace -
 Polymorphic attacks: the shape-shifting threat
Polymorphic attacks: the shape-shifting threat -
 ‘Lost’ zip design could give space exploration a lift
‘Lost’ zip design could give space exploration a lift -
 Orbitae - AI by SDG Group launches Gena Suite to scale enterprise AI
Orbitae - AI by SDG Group launches Gena Suite to scale enterprise AI -
 Firms ‘wasting AI’ by using it to speed up bad habits
Firms ‘wasting AI’ by using it to speed up bad habits -
 Why leadership matters when implementing AI
Why leadership matters when implementing AI -
 Stratospheric telecoms blimp completes “historic” record 12-day flight over Atlantic
Stratospheric telecoms blimp completes “historic” record 12-day flight over Atlantic -
 Mobile operators warn of higher bills and slower 5G rollout after energy support exclusion
Mobile operators warn of higher bills and slower 5G rollout after energy support exclusion -
 The 2026 European awards cement Steve Durbin and the ISF at the forefront of cybersecurity
The 2026 European awards cement Steve Durbin and the ISF at the forefront of cybersecurity -
 These are the 10 AI trends to watch in 2026 that will drive business forward
These are the 10 AI trends to watch in 2026 that will drive business forward -
 Europe launches ‘anti-kill switch’ cloud shield as Trump fears grip Brussels
Europe launches ‘anti-kill switch’ cloud shield as Trump fears grip Brussels -
 Starmer summons social media chiefs to Downing Street over child safety
Starmer summons social media chiefs to Downing Street over child safety -
 AIMi: bringing intelligence and speed to data migration
AIMi: bringing intelligence and speed to data migration -
 GITEX Africa Morocco to host 1,450 exhibitors and startups as Marrakech event sharpens focus on AI and digital sovereignty
GITEX Africa Morocco to host 1,450 exhibitors and startups as Marrakech event sharpens focus on AI and digital sovereignty -
 EXCLUSIVE: LA unveils Ghostbusters-style car to fight post-wildfire ‘toxic soup’
EXCLUSIVE: LA unveils Ghostbusters-style car to fight post-wildfire ‘toxic soup’ -
 Social media giants hit with $6m verdict in landmark youth harm case
Social media giants hit with $6m verdict in landmark youth harm case -
 Former Google executive launches €50m fund targeting Europe’s deep tech scale-up gap
Former Google executive launches €50m fund targeting Europe’s deep tech scale-up gap -
 Airbus to acquire Ultra Cyber in UK defence cyber expansion
Airbus to acquire Ultra Cyber in UK defence cyber expansion -
 UK exposed by cyber omission in Spring Statement as threats intensify, ISF chief warns
UK exposed by cyber omission in Spring Statement as threats intensify, ISF chief warns