Managing risk across the supply chain

John E. Kaye
- Published
- Home, Technology

Managing risk in your supply chain and protecting data privacy has become crucial in our interconnected world – a task that is complex, ongoing, and best achieved with expert help
It is a simple fact that no business can exist without customers and vendors. And, as the global economy grows ever more reliant on digital processes at every point of the supply chain, we are witnessing an exponential increase in the amount of data that must be shared to effectively service customers.
It is therefore important for information leaders to understand that when they move data into the supply chain, they are still responsible for that data. The consequences and penalties of mismanaging and not keeping track of sensitive information can be severe both in financial terms (fines for breaking data privacy regulations) and reputational damage (losing your customers’ trust). Welcome to the world of vendor risk management (VRM).
Diligent vendor risk management is all about making sure that you share data with competent, trustworthy suppliers and vendors who treat your digital assets with the utmost care and professionalism. However, accidents will still happen, but by implementing good data security processes and ensuring people are trained and aware of the threats, the risk is significantly reduced. Phishing emails are causing increasing problems with ransomware seen recently across many industries. Often these attack supply chain partners and your vendors, using them as an easy “back door” into client systems.
Data security specialists break this down into three elements: people, process, and technology. Yet the inner workings of any given company are not plain to see, meaning weaknesses are all too often hidden from view – the devil is truly in the details. So, how do you assess a supplier against these criteria?
The COBRA solution
A recent survey conducted in the US found that 44% of organisations had suffered a third-party breach in the past 12 months, and 74% of those said the incident came about because they gave up too much privileged access. Yet, many organisations, especially larger ones, still think they should undertake VRM in-house. Whilst they may be experts in their own specific field, they often underestimate the multifaceted approach required to “assure” their supply chain. Cyber security experts C2 Cyber use a bespoke VRM solution, COBRA, to help businesses answer the following questions:
- Where are my largest risks and what is causing them?
- What is undermining my resilience?
- What can I do to improve the situation?
- How much have I reduced risk over the last year?
C2’s managed service allows organisations to answer these questions with confidence, and focus their resources on collaborating to reduce risk, rather than being overwhelmed by assessing it. Risk assessment in itself delivers little value without the systems and insight required to act on findings. This is where COBRA comes into its own: it illuminates your organisation’s risk landscape and provides quick access to the areas that need action. COBRA does the heavy lifting, empowering your team by releasing them from the labour intensive processes so often associated with risk assessment.
COBRA provides the certainty, support and stability that information leaders crave. In the words of one CISO of a global luxury fashion brand: “The C2 team have simplified the process of our vendor risk management, whilst increasing the responsiveness and accuracy of our programme. Their COBRA service supports the business sponsors, procurement and legal teams as well as the vendors themselves and assures our information is secure.
With their collaborative approach, it felt like we had a partner standing with us shoulder to shoulder, making the integration of their managed service a positive experience across the business.”
Fluid and agile
One of the crucial aspects of C2’s solution is that it recognises that risk is not static. The company’s open source intelligence continuously tracks risk indicators, identifying changes that could impact on the business. With risk identified and recommendations made, COBRA then provides a secure framework to allow all businesses, suppliers, and security stakeholders to work together and target high-risk areas. It quite literally puts everyone on the same page. And this all happens at speed, reflecting the constantly shifting threat landscape.
C2’s approach is collaborative, their team doesn’t seek to only show suppliers where the vulnerabilities lie, but recommends technological processes or fixes and offers constructive advice on where a client’s in-house skills and training could be improved.
According to Jonathan Wood, CEO of C2 Cyber, operating a collaborative third party risk management programme isn’t all about preventing against negative outcomes. There are positive reasons for doing so, and the company’s expert input resonates right down the value chain: “Assuring your supply chain allows vendors to demonstrate to their customers how seriously they take security. It also improves staff retention. Investment in people’s cyber security knowledge builds confidence internally within an organisation, and again, customers note this. A positive ecosystem is created based on confidence, trust and professionalism,” says Wood.
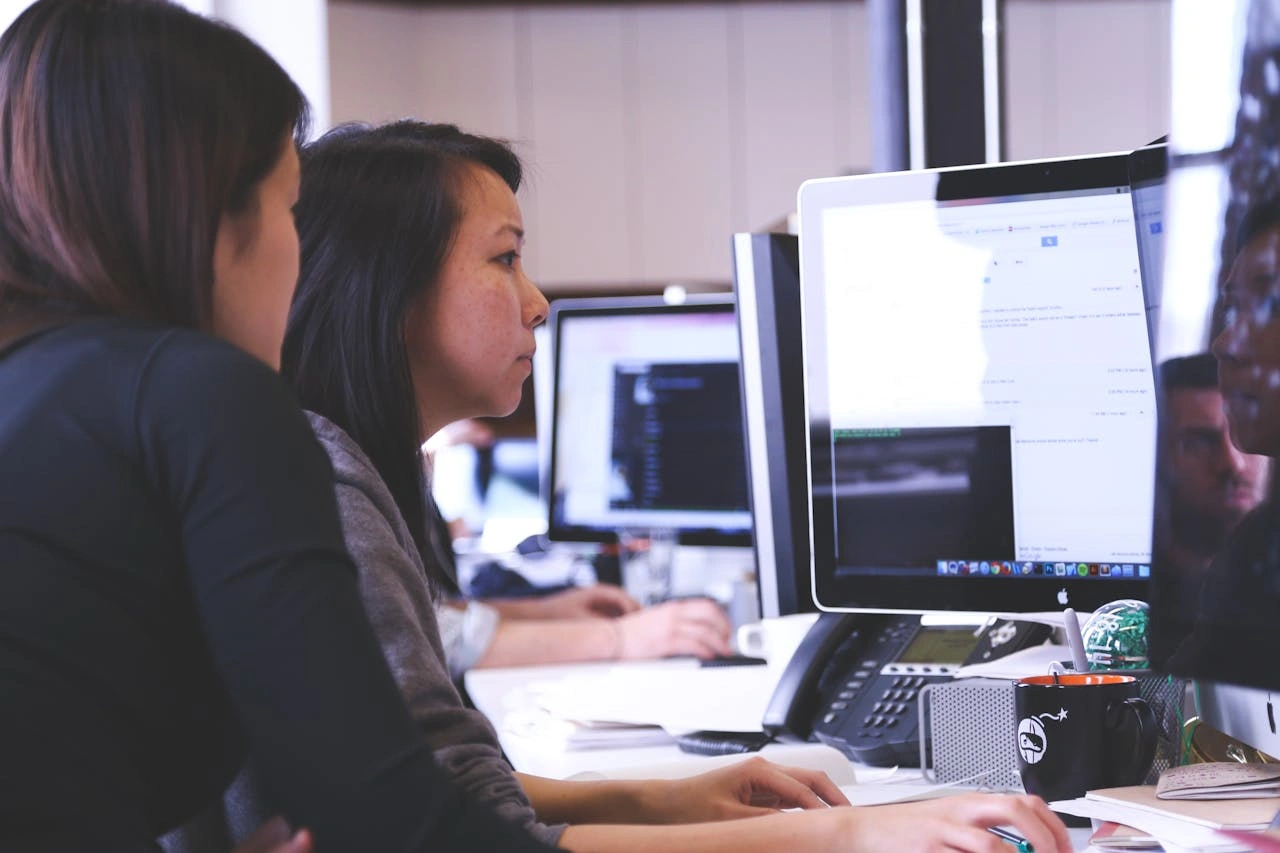
Control of a remote world
According to a recent study by McKinsey, one-third of work in Europe’s leading economies could continue to be done remotely, even after the pandemic subsides. This shift in working practices brings with it new circumstances and vulnerabilities. Data that was once locked away or accessed from a central location is now in people’s homes, which increases the size of the target for cyber threat actors. This is an area that C2 understands well. Over the last year they have been working with their clients to not only secure this data internally, but also within their supply chains. C2 reviews an organisation’s policies and looks at the systems by which they share data, helping to implement better working practices. In today’s interconnected world, this reflects a level of insight and support that forward-thinking companies cannot afford to be without.
What is your VRM strategy?
C2 Cyber believes it has the only fully integrated vendor risk management platform on the market, providing an end-to-end service that demonstrates true reductions in vendor risk by leveraging true accountability. C2’s online supplier security assessments achieve a 99% completion rate in 40% of the time versus traditional methods, and reduce customer costs by 50% on average. The suppliers actually seem to appreciate the feedback, and the collaborative, constructive recommendations they receive.
Most importantly, the process is objective. This isn’t just about measuring risk. It’s enabling true accountability in both your business and your suppliers, and working towards true remediation of risk.
Further information
RECENT ARTICLES
-
 Stratospheric telecoms blimp completes “historic” record 12-day flight over Atlantic
Stratospheric telecoms blimp completes “historic” record 12-day flight over Atlantic -
 Mobile operators warn of higher bills and slower 5G rollout after energy support exclusion
Mobile operators warn of higher bills and slower 5G rollout after energy support exclusion -
 The 2026 European awards cement Steve Durbin and the ISF at the forefront of cybersecurity
The 2026 European awards cement Steve Durbin and the ISF at the forefront of cybersecurity -
 These are the 10 AI trends to watch in 2026 that will drive business forward
These are the 10 AI trends to watch in 2026 that will drive business forward -
 Europe launches ‘anti-kill switch’ cloud shield as Trump fears grip Brussels
Europe launches ‘anti-kill switch’ cloud shield as Trump fears grip Brussels -
 Starmer summons social media chiefs to Downing Street over child safety
Starmer summons social media chiefs to Downing Street over child safety -
 AIMi: bringing intelligence and speed to data migration
AIMi: bringing intelligence and speed to data migration -
 GITEX Africa Morocco to host 1,450 exhibitors and startups as Marrakech event sharpens focus on AI and digital sovereignty
GITEX Africa Morocco to host 1,450 exhibitors and startups as Marrakech event sharpens focus on AI and digital sovereignty -
 EXCLUSIVE: LA unveils Ghostbusters-style car to fight post-wildfire ‘toxic soup’
EXCLUSIVE: LA unveils Ghostbusters-style car to fight post-wildfire ‘toxic soup’ -
 Social media giants hit with $6m verdict in landmark youth harm case
Social media giants hit with $6m verdict in landmark youth harm case -
 Former Google executive launches €50m fund targeting Europe’s deep tech scale-up gap
Former Google executive launches €50m fund targeting Europe’s deep tech scale-up gap -
 Airbus to acquire Ultra Cyber in UK defence cyber expansion
Airbus to acquire Ultra Cyber in UK defence cyber expansion -
 UK exposed by cyber omission in Spring Statement as threats intensify, ISF chief warns
UK exposed by cyber omission in Spring Statement as threats intensify, ISF chief warns -
 Unclear AI rules risk driving talent away from UK employers, survey suggests
Unclear AI rules risk driving talent away from UK employers, survey suggests -
 Global fraud summit told AI scams and sextortion are driving industrial-scale crime
Global fraud summit told AI scams and sextortion are driving industrial-scale crime -
 AI boom leaves many workers without the data skills employers now need
AI boom leaves many workers without the data skills employers now need -
 Cybersecurity becomes Britain’s most sought-after tech skill as pay and hiring surge
Cybersecurity becomes Britain’s most sought-after tech skill as pay and hiring surge -
 AI now trusted to plan holidays more than work, shopping or health advice, survey finds
AI now trusted to plan holidays more than work, shopping or health advice, survey finds -
 Could AI finally mean fewer potholes? Swedish firm expands road-scanning technology across three continents
Could AI finally mean fewer potholes? Swedish firm expands road-scanning technology across three continents -
 Government consults on social media ban for under-16s and potential overnight curfews
Government consults on social media ban for under-16s and potential overnight curfews -
 Twitter co-founder Jack Dorsey cuts nearly half of Block staff, says AI is changing how the company operates
Twitter co-founder Jack Dorsey cuts nearly half of Block staff, says AI is changing how the company operates -
 AI-driven phishing surges 204% as firms face a malicious email every 19 seconds
AI-driven phishing surges 204% as firms face a malicious email every 19 seconds -
 Deepfake celebrity ads drive new wave of investment scams
Deepfake celebrity ads drive new wave of investment scams -
 Europe eyes Australia-style social media crackdown for children
Europe eyes Australia-style social media crackdown for children -
 Europe opens NanoIC pilot line to design the computer chips of the 2030s
Europe opens NanoIC pilot line to design the computer chips of the 2030s